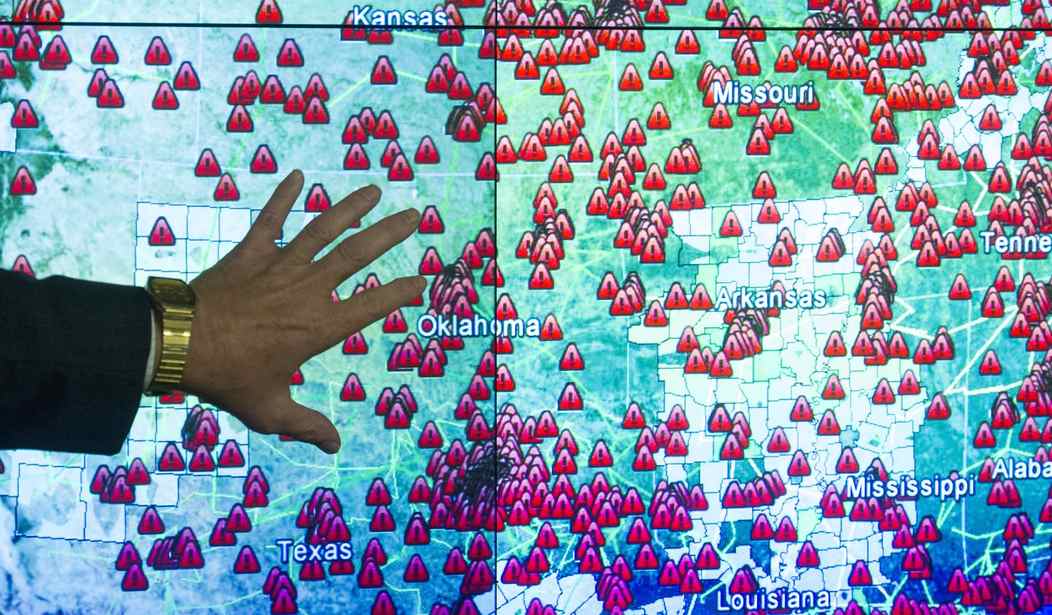
2021 was in many ways the year of the cyberattack, as there were more attacks and total dollars paid out in ransoms than any other year in history.
New ransomware strains and the rise of state-sponsored hacking outfits, including Advanced Persistent Threat Groups (APTs), will almost certainly make 2022 an even more difficult year for information technology professionals working to keep computer systems safe.
Despite new programs created by the Department of Homeland Security (DHS) and the Cybersecurity and Infrastructure Security Agency (CISA), 2021 ended similarly to the way it began — with America paying catch-up in the cybersphere. Here were some of 2021’s most critical cybersecurity moments:
-
- January: Former Director Christopher Krebs of the Cybersecurity and Infrastructure Security Agency (CISA), is hired by SolarWinds, victim of perhaps the most wide-ranging hacking attack ever. Krebs had been fired by President Trump after his endorsement of a statement from the Elections Infrastructure Government Coordinating Council and the Election Infrastructure Sector Coordinating Executive Committees claiming that the Nov. 3 election was “the most secure in American history.” The statement fails to acknowledge the Hall County, Ga., ransomware attack that disabled the county’s voter signature database.
- February: New DHS programs focused on improving American cybersecurity via increased funding for state and local governments through Federal Emergency Management Agency (FEMA) grants and “The Reduce the Risk of Ransomware Campaign,” are announced.
- March: One of the year’s most notorious attacks targets Microsoft Exchange Server software and offers hackers access to the email accounts of more than 30,000 US entities. The attack is carried out by the Chinese Advanced Persistent Threat Group Hafnium. The aftermath sees Joe Biden and our European allies threaten economic sanctions against the Chinese government for the hack, although none have come down as of Dec. 31, 2021.
- April: Russia’s DarkSide Ransomware Group executes what was probably the most economically damaging attack of 2021, the Colonial Pipeline Ransomware Attack. Although it was not actually reported until May, the attack is initiated in late April and eventually shuts down a 5,500-mile pipeline responsible for the delivery of 45% of the east coast’s fuel.
- May: More supply chain issues for the US, as a major hack targets meat manufacturer JBS Foods. The Russian-based group known as the REvil Ransomware Gang slows beef distribution in America this past spring before receiving $11 million from JBS.
- June: Colonial Pipeline CEO, Joseph Blount, appears in front of Congress to field questions regarding the DarkSide hack. The question of whether Colonial violated the 2020 Office of Foreign Assets Control (OFAC) advisory outlining penalties for businesses that are found to have issued ransom payments to groups or individuals under U.S. sanctions is addressed, among other matters related to the attack.
- July: REvil targets IT infrastructure provider Kaseya with a phony software update that targets Kaseya’s clients. The hackers claim that up to one million organizations or individuals have their computers encrypted and REvil demands $70 million in bitcoin from Kaseya.
- August: CISA announces the formation of the Joint Cyber Defense Collaborative. The program leverages the expertise of “Big Tech” companies Google, Amazon, and Microsoft in assisting the federal government in its efforts to protect critical infrastructure against future attacks.
- September: Labor Day weekend sees a ransomware attack target historically black Howard University. The hack disrupts online classes for almost a week.
- October: Microsoft reports in an Oct. 24 blog post that Russian APT group Nobelium, who many believe is responsible for the SolarWinds attack, spent three months attacking entities that resell Microsoft cloud services. Just in time for Halloween, candy manufacturer Ferrara is victimized by a ransomware attack.
- November: Foreign cyber criminals breach nine entities in the education, defense, healthcare, energy, and technology sectors.
- December: The Abraham Accords, which were brokered by the Trump administration, lead to a historic deal being struck between the United Arab Emirates and Israel to share defense and cyber intelligence. A new CISA advisory warns of a vulnerability that potentially threatens the security of hundreds of millions of devices. The vulnerability, which is known as Log4j, is part of a utility that runs on many common software applications.
2022 should only see more new attacks as the stakes continue to rise in the ongoing global cyberwar. The new year is also sure to see new ransomware strains and the creation of more state-sponsored Advanced Persistent Threats (APTs) as the Biden administration scrambles to attempt to respond, and with the mid-term election less than a year away, the question of their competence in dealing with these emerging threats is sure to play a key role in the minds of voters.








Join the conversation as a VIP Member