Department of Defense had been using eight-inch floppy disks – a 53-year-old technology – to coordinate some of its nuclear forces.
Other mind-boggling discoveries detailed in the GAO report included Treasury’s use of a 56-year-old program to retain tax records, Veterans Affairs’ 53-year-old timekeeping and payroll system, Justice’s 35-year-old program for keeping certain inmate records and the Social Security Administration’s 31-year-old system for determining retirement benefits. This is all despite the fact that the federal government spends about $90 billion annually on major information technology acquisition.
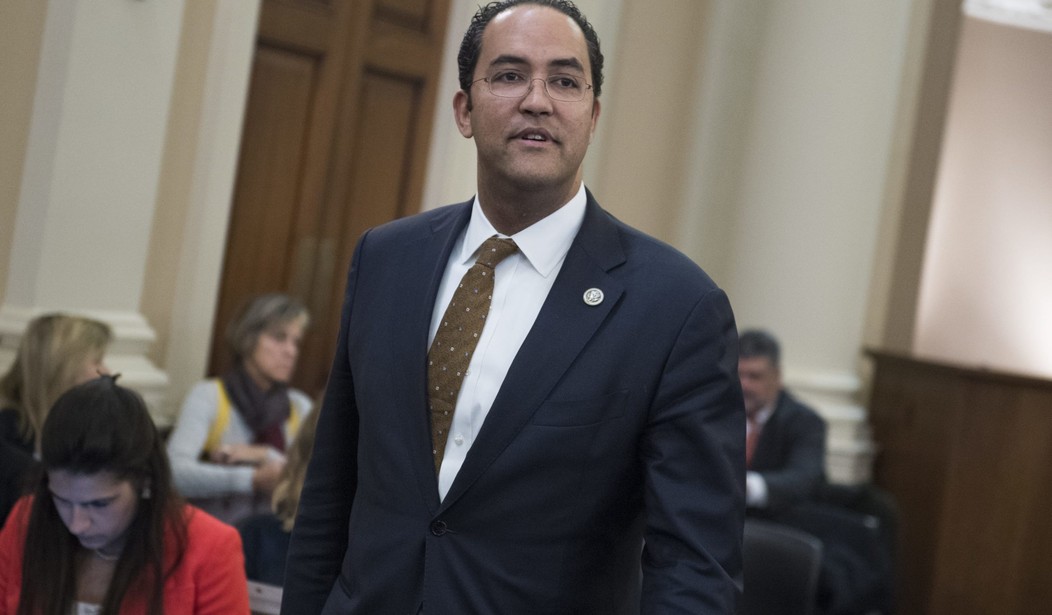
Rep. Will Hurd (R-Texas), a former CIA operations officer, said on Friday that the U.S. continues to lag when it comes to good “IT system hygiene” and basic federal housekeeping, which is concerning given the rise of quantum computing and the role it is expected to play in national security. Quantum computing is supposed to usher in a new era of computing, allowing classic computers to complete new, highly complex tasks.
“It is going to upend and change how we do encryption. It is going to change how we operate in the digital space,” Hurd said at the Center for Strategic & International Studies.
Russian President Vladimir Putin said in September that the nation that masters artificial intelligence will become “the ruler of the world.” On modern warfare, he said that “when one party’s drones are destroyed by drones of another, it will have no other choice but to surrender.” Hurd agreed with Putin’s assessment.
“The true hegemon is going to be based on quantum computing, and we have to make sure we’re doubling down on basic research,” Hurd said. “We have to make sure that we’re understanding this technology because it’s going to be here sooner than we expect.”
Hurd described how a high-ranking official at the Social Security Administration, whom he did not name, recently testified before House lawmakers about vulnerabilities. Despite the assessment, the official could not tell lawmakers how many vulnerabilities and critical vulnerabilities the U.S. faces. Hurd said there was no plan in place for how to defend U.S. digital infrastructure.
“So we have to make sure we have the right people in these positions,” he said.
According to the GAO, there are about 15,000 unfilled positions in the federal government. The Modernizing Government and Technology Act, which has passed in the House but awaits consideration in the Senate, would direct agencies to formulate plans to modernize IT systems. Though Hurd said the House is “not ready to spike the football yet” and celebrate passage of the legislation, he described how he envisions a modern federal workforce.
He said that the U.S. should build a cyber threat defense force, in which recent graduates will work at federal agencies then inevitably move to the private sector, and the companies will loan employees back to the federal government on an intermittent, short-term basis. The U.S., he said, needs to develop a plan — fast.
“If the North Koreans launched a missile into Equifax headquarters, we all know how we would respond, right?” he said. “But the theft of all their information, all y’alls information, nobody in here opted into a credit-monitoring system, but that information is going to ultimately be used against us. It has shaken the foundations of authentication because we do so much authentication based on what you find in that credit report, and now guess what. Somebody has it. So they’re going to be able to spoof you. Is that an act of war?”
These questions, he said, are being discussed in various facets of Congress and government, but the U.S. does not yet have a national strategy. If the legislation passes the Senate, he said, these will be questions that lawmakers and agency heads will need to grapple with in the coming few weeks and months.







Join the conversation as a VIP Member