Hackers initiated a ransomware attack yesterday that infected thousands of computers in nearly 100 countries, including hospitals and other key infrastructure systems. Experts are calling it one of the largest cyber attacks in history.
The cyber criminals used part of a malicious code that was reportedly developed by the U.S. National Security Agency and published online last month by a previously unknown group called “The Shadow Brokers.”
Cyber extortionists tricked victims into opening malicious malware attachments to spam emails that appeared to contain invoices, job offers, security warnings and other legitimate files.
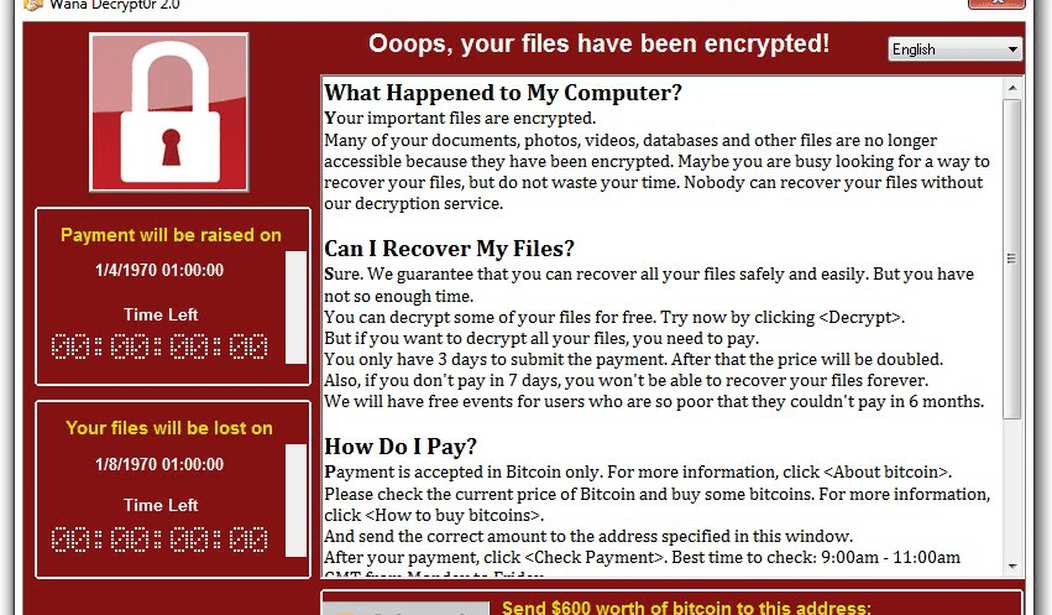
The ransomware encrypted data on the computers, demanding payments of $300 to $600 to restore access. Security researchers said they observed some victims paying via the digital currency bitcoin, though they did not know what percent had given in to the extortionists.
Researchers with security software maker Avast said they had observed 57,000 infections in 99 countries, with Russia, Ukraine and Taiwan the top targets.
Some experts said the threat had receded for now, in part because a British-based researcher, who declined to give his name, registered a domain that he noticed the malware was trying to connect to, limiting the worm’s spread.
“We are on a downward slope, the infections are extremely few, because the malware is not able to connect to the registered domain,” said Vikram Thakur, principal research manager at Symantec.
“The numbers are extremely low and coming down fast.”
But the attackers may yet tweak the code and restart the cycle. The British-based researcher who may have foiled the ransomware’s spread told Reuters he had not seen any such tweaks yet, “but they will.”
Finance chiefs from the Group of Seven rich countries will commit on Saturday to join forces to fight the growing threat of international cyber attacks, according to a draft statement of a meeting they are holding in Italy.
“Appropriate economy-wide policy responses are needed,” the ministers said in their draft statement, seen by Reuters.
While the hackers only asked for $300-600, when multiplied by 57,000 computers, the amount they could have potentially stolen was significant. But was money the object of the attack, or was it the beginning of even more mischief where they might try to hold entire countries hostage? Great Britain’s National Health Service was actually forced to turn away patients because their computers were inoperative. That kind of potential damage should frighten governments to the point where they would be willing to pay just about anything to avoid the disruptions.
The hackers, who have not come forward to claim responsibility or otherwise been identified, likely made it a “worm,” or self spreading malware, by exploiting a piece of NSA code known as “Eternal Blue” that was released last month by a group known as the Shadow Brokers, researchers with several private cyber security firms said.
“This is one of the largest global ransomware attacks the cyber community has ever seen,” said Rich Barger, director of threat research with Splunk, one of the firms that linked WannaCry to the NSA.
The Shadow Brokers released Eternal Blue as part of a trove of hacking tools that they said belonged to the U.S. spy agency.
Microsoft said it was pushing out automatic Windows updates to defend clients from WannaCry. It issued a patch on March 14 to protect them from Eternal Blue.
“Today our engineers added detection and protection against new malicious software known as Ransom:Win32.WannaCrypt,” Microsoft said in a statement on Friday, adding it was working with customers to provide additional assistance.
There is little doubt that our browsers and operating systems are highly vulnerable to attack. But it still comes down to basic security protocols: don’t open emails or click on links from unknown senders. Until most of us learn this vital lesson, the hackers will continue to be successful in penetrating our systems.








Join the conversation as a VIP Member